Softaculous Auto Installer
We are pleased to announce the release of the Softaculous Auto Installer plugin, officially named Soft Auto Installer for Blesta. In conjunction with our cPanel module, the plugin allows hosting providers to sell application hosting by provisioning WordPress, Drupal, Joomla, or any other supported application through Softaculous with a new hosting plan. Support for Plesk and DirectAdmin is on the way.
Watch the video below for more information, and be sure to check out the documentation for details on usage. The plugin should be included with Blesta 4.5 which is soon to be in beta, and can be obtained from our Github for use on version 4.4+ right now.
“The Auto install script feature in Blesta using the Softaculous plugin will help web hosts to configure specialized hosting packages like WordPress Hosting, Joomla Hosting, etc. Blesta’s easy to use admin panel allows the admin to install and configure the plugin in just couple of minutes.” - Pulkit Gupta, CEO, Softaculous Ltd
How does it work?
- The plugin registers with the Event system in Blesta
- The plugin watches for cPanel services that are provisioned that have specific config options
- The plugin makes an API call to Softaculous within cPanel to install the desired application
This plugin opens the doors wide for Blesta users to offer application hosting of many different types. See the full list of supported applications with Softaculous, and consider installing Softaculous on your WHM server if you haven’t already.
Related Tags:
Blesta 3.0: Software Licensing
Software licensing offers software developers a means of ensuring their product is not installed without prior authorization (generally by purchasing the product). Some competing products offer licensing modules to facilitate the deployment of such software, but their designs are critically flawed in a number of ways. Today I’ll describe the software licensing scheme we use in Blesta 3.0, and why it works. But first, let’s take a look at the problem.
To ensure an installation is allowed to run it needs to established its authenticity. This is generally done by “calling home.” That is, by contacting the licensing server. Information returned from the licensing server varies, but generally contains data about how, when, and where the software can run.
The naive approach
It goes without saying that if the license data can be tampered with one can easily bypass the license check. To resolve this, others have devised a scheme whereby the data is hashed using a shared secret salt know by the licensing server and by the product. When the product receives the license data it creates a hash from the data using the shared secret salt and compares that hash with the one that accompanied the data. If the two hashes match the data is trusted, otherwise the data is rejected.
Some systems don’t even bother sending the original hash of the data and instead compute and store the hash upon arrival for future reference. These systems are even less secure.
There are a number of exploits with these systems:
- Because the same shared secret is used to generate the hash across all installations it may be possible to obtain the shared secret
- Because the hashing method generally used is insecure it may be possible to tamper with the data and still produce the same hash (i.e. a hash collision)
- Because the data passed across the line is unencrypted or poorly encrypted it may be intercepted and the licensing server may be tricked into returning data regarding a separate valid license, or the licensing server may itself be spoofed
Exploiting it
Some may argue the dangers of revealing how insecure systems can be compromised, just as a magician might jeer at the sight of someone exposing their trickery. Those that argue from that position fail to realize that security does not arise out of obfuscation. Shannon’s maxim teaches that one must always assume that an attacker understands exactly how a system operates.
- Determine where the software calls home to. This can be done by monitoring network traffic or guessing the license server domain.
- Spoof the licensing server by modifying the server’s DNS or hosts file to resolve to a “license server” you create.
- Capture the data sent to the licensing server to a log file.
- Capture the data returned from the licensing server. This can be done by manually passing the data from #3 to the licensing server. Note that if you do not have information to obtain a valid response from the license server, you may be able to obtain that information from another user with a valid license or from a public demo of the application.
- Return the license data you capture from the license server, or modify it to ensure it continues to function ad infinitum.
The solution
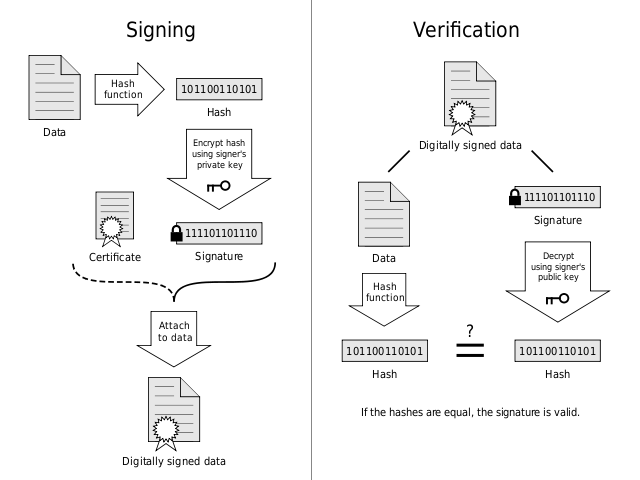
A digital signature allows us to verify the authenticity of a message through the use of an asymmetric key cipher, which uses one key (the private key) to encrypt data and an entirely different key (the public key) to decrypt data. Meaning that an attacker can not reproduce signature data since they do not have the private key.
How it works
- The license server generates a unique public/private key pair for the installation and delivers the public key securely to the installation
- The license server then encrypts the license data, generates a hash of the data and encrypts it using the private key to produce the signature
- The license server then delivers the data and signature to the installation
- The installation verifies the signature by decrypting the signature with the public key and comparing it with the hash it generates from the data
In the event that the signature can not be verified the license data is rejected and the license becomes invalid. Attempting to spoof the license server does nothing because only the license server can sign messages and the installation will only be able to verify signatures from the license server.
Additionally, at any time the license server may choose to generate a new key pair. This is especially useful because as attacks on asymmetric key ciphers becomes computationally cheaper it becomes increasingly important to cycle keys and/or increase key lengths.
Why are we telling you all this?
It would be great if there were no need for software license validation, but there is and there’s a market for it. Our philosophy is if you’re going to do something you ought to do it right. At the moment, thousands of developers put their software in the hands of licensing systems that provide illusory protection at best, and that’s unfortunate.
So, why are we telling you all this? Because we’re building a licensing plugin for v3 that does it right. We don’t mind sharing with everyone how it works because even licensing systems should be transparent. And, if our competitors decide to rework their licensing systems and do things right — then everyone is better off. And that’s what it’s all about.
Blesta 3.0: Plugins
So, let’s keep it real. I didn’t have the time to make a video this week. I’ve been doing a lot of graphic design work on Blesta, some awesome stuff you’ll get to see soon. But that doesn’t mean I can’t share something, right?
Plugins. Are. Amazing. Plugins can do a lot, we’ve talked about them before in passing while describing other features. Plugins can register widgets on the Dashboard, on the Billing Overview, on the Client Profile. Plugins can create entirely new pages, with new functionality, with their own nav links. Plugins can register themselves into the ACL. Plugins can create their own email templates. Plugins are mini-applications. Plugins are POWERFUL.
I know people are going to shock us with what they develop for Blesta using the plugin system. I can’t wait to be blown away.
This post is the tip of the tip of the iceburg, we will have a lot more to say about plugins as we get closer to release.
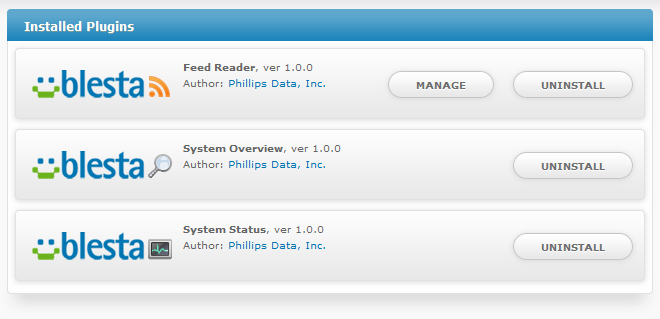
Oh yeah, plugins can be installed, and uninstalled, upgraded and managed. Here’s what the installed plugins window looks like. These are all plugins that will come pre-installed with Blesta (there will be more too, don’t worry). These ones create widgets on the Dashboard.. and since we wrote them, they got slapped with the Blesta logo. Slap your logo on your own plugin!
Maybe a video next week? We’ll see!
